What Is AES Encryption and How Does It Work?
In a world where malicious hackers are looking for opportunities to steal or destroy data, encryption has become an essential part of the digital world. Encryption is a way of protecting data by scrambling it so that only authorized persons with the secret key can decrypt and read it. AES is an encryption algorithm that VPN service providers and government agencies widely use to protect data. This article dwells on AES encryption and how it works.
What Is AES Encryption?
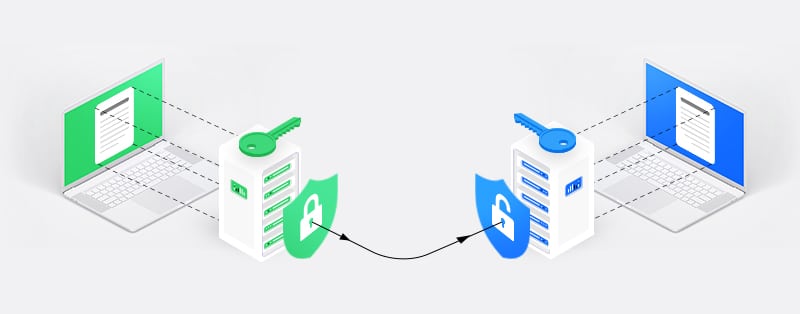
There are two main types of encryption: Symmetric and Asymmetric. Asymmetric encryption involves using two different keys (private and public) to encrypt and decrypt data, while symmetric encryption involves using a single key for encryption and decryption. Advanced Encryption Standard (AES) belongs to the symmetric category of encryption. It is a subset of the Rijndael family of symmetric block ciphers developed by Vincent Rijmen and Joan Dae in 1998, hence the name “Rijndael.”
AES is an iterative cipher based on the substitution permutation network (SPN) algorithm. The SPN algorithm is a class of block ciphers that involves rounds of a repeated series of mathematical operations. It is due to these encryption rounds that AES is a formidable encryption cipher. AES has three different types based on the length of the encryption keys. They include AES-128, AES-192, and AES-256.
The key length of each of these types of AES determines their strength; the longer the length, the stronger the encryption. The 128-bit and 192-bit AES encryption cipher have 3.4 x 1038 and 6.2 x 1057 possible key combinations, respectively. AES-256 is the most robust encryption cipher and has 1.1 x 1077 possible key combinations. Despite the variance in key length, AES’s block size always remains the same–128 bits.
Why Was AES Developed?
Earlier encryption ciphers were simpler, and with the right amount of time and tools, anyone could crack them. As technology kept on advancing, hackers had better tools at their disposal to battle encryption ciphers. It was apparent that encryption ciphers needed to be more sophisticated than what existed at that moment, which was the Data Encryption Standard (DES).
Like AES, DES is also a symmetric-key algorithm. IBM developed DES in the 1970s, and the US National Bureau of Standards (NBS) adopted it as the standard encryption cipher for encrypting sensitive government information. Due to its adoption by the NBS and US government, different sectors accepted DES. It also piqued the academic community’s interest, which spurred an interest in the study of cryptography. For decades, DES proved to be formidable until June 1997 where the DESCHALL group publicly cracked it.
The Electronic Frontier Foundation’s (EFF) DES cracker performed the same feat in 56 hours in the following year. In 1999, it took less than 24 hours to break a DES key. These significant events showed that with increasing computing power and advancement in technology, it would only be a matter of time before cracking the DES became easy to do. Besides, the DES key length did not exceed 56-bits compared to the all-powerful 256-bit AES.
In 2001, the National Institute of Standards and Technology (NIST) revealed its adoption of the AES encryption cipher because of its all-round capabilities. It is better than DES performance-wise, easy to implement, and extremely difficult to break.
How Does AES Encryption Work To Protect Your Data
Understanding the AES encryption algorithm can be challenging if you don’t have a proper mathematics background. However, we will try to simplify the process for you to have a basic understanding of how it works. The AES encryption algorithm encrypts and decrypts data in blocks of 128 bits. Despite the variation in key length, the block size doesn’t change.
The AES encryption algorithm combines a secret key (128, 192, or 256-bit key) with plain text (sensitive data you want to encrypt) to create a cipher. The AES cipher uses a series of mathematical transformations (substitution-permutation) using the secret key and plain text. Before any operation occurs, the plain text data is separated into a 4 x 4 matrix of sixteen bytes or 128 bits (one byte equals 8 bits) since AES encrypts data in blocks of bits.
The AES algorithm uses substitution-permutation with several rounds to convert plaintext data to a final ciphertext. The key size determines the number of rounds. A 128-bit key size has ten rounds, a 192-bit key size has twelve rounds, and a 256-bit key size has fourteen rounds. Now, let’s take a look at the operations involved in the process of converting plaintext data to ciphertext.
1. Key Expansion and AddRoundKey
In this operation, AES uses the Rijndael Key Schedule to produce new 128-bit round keys (subkey) from the primary secret key. That is, it involves using the initial secret key to create a series of keys for each round of the encryption operation. In the AddRoundKey operation, each byte of the current data state is mixed with a byte of the current round key utilizing a bitwise XOR operation.
2. SubBytes (substitute bytes)
In this operation, the 16-byte block is run through a Rijndael substitution box (S-Box) to give an alternate value for each byte. Each byte is substituted according to rules prescribed by the predefined Rijndael S-Boxes. The S-box takes a value and replaces it with another value. The process is much more complicated, but it makes breaking the AES cipher nearly impossible with the computing resources in the world.
3. ShiftRows
The ShiftRows operation shifts all rows in a 16-byte block except the first one. It is easier to understand compared to the SubBytes operation. The first row does not change and remains the same. The second row moves to the left by one byte, the third row moves to the left by two bytes, and the fourth row moves to the left by three bytes.
4. MixColumns
This operation transforms each column in the 16-byte block linearly. Due to how complicated this operation can be, we will not dwell too much on it. Using matrix multiplication and bitwise XOR addition, this operation multiplies each column with a predefined 4 x 4 matrix resulting in a new column and block.
Order of Operations
Every data that AES encrypts must pass through each of the operations above. These operations are repeated multiple times depending on the number of rounds required. A 128-bit key requires ten rounds, a 192-bit key requires twelve rounds, and a 256-bit key requires fourteen rounds. Below, we will take a look at the order in which these operations execute to encrypt data.
1. Key Expansion
2. AddRound
3. The following operations will go on for 9, 11, 0r 13 rounds in the order below:
SubBytes
ShiftRows
MixColumns
AddRound
4. The following operations take place in the last round (10th, 12th, or 14th depending on the secret key’s length):
SubBytes
ShiftRows
AddRound
Decrypting AES Encryption
We have seen how AES encrypts data, but how does it decrypt data? The decryption process is simple. Reversing all the steps involved in the encryption process will decrypt data. Let’s take a look at how the process would be if we were decrypting data.
1. The following operations take place in the last round 10th, 12th, or 14th depending on the secret key’s length):
Inverse AddRound
Inverse ShiftRows
Inverse SubBytes
2. The following operations will go on for 9, 11, or 13 rounds in the order below:
Inverse AddRound
Inverse MixColumns
Inverse ShiftRows
Inverse SubBytes
Inverse AddRound
Does AES Encryption Have Security Issues?
Although there have been no recorded successful attacks on AES encryption, wrongly implementing it can lead to hackers discovering a vulnerability and exploiting it. Since cryptographers are always looking for vulnerabilities on AES, there have been a few successful theoretical and side-channel attacks. Let’s look at a few of them.
1. Known-Key Distinguishing Attack
In 2009, an attempt to crack the 8-round version of AES-128 with a known-key distinguishing attack was successful. Since AES-128 has ten rounds of encryption, it is still impenetrable. Also, an attacker has to know the encryption key before it can work, which is highly unlikely.
2. Side-Channel Attacks
Side-channel attacks will only work if someone doesn’t correctly implement AES encryption because it relies on a system leaking information. The attacker pays attention to data leaks like electromagnetic information, power consumption, timing information, etc., to gather information from the algorithm. AES is not entirely immune to this type of attack.
3. Other Attacks
Other attacks that cryptographers have tried to use to break AES encryption include key-recovery attacks and related-key attacks. In both cases, the attacker targets the encryption key. In a key-recovery attack, the attacker needs to have at least a pair of encrypted and decrypted messages. In a related-key attack, the attacker needs to know the relationship between two different keys. These attacks only work on systems that incorrectly implement AES and are not significant threats.
Conclusion
The primary reason why security agencies and top VPN services use AES encryption is because of its immunity to attacks. Asides from being practically impossible to break, the Advanced Encryption Standard is fast, versatile, and easy to implement. Compared to other encryption types like DES, it also uses less memory. You can also combine it with other security protocols to ensure a high level of security.
Join the TechRobot Newsletter
Actionable tips on online security, the best VPNs, unblocking guides, and special offers — straight to your inbox.